提醒:本文最后更新于 3526 天前,文中所描述的信息可能已发生改变,请仔细核实。
 自打脱离WP 8.1,我就不用L2TP了,奈何鬼娃娃(林友赛)找我。
自打脱离WP 8.1,我就不用L2TP了,奈何鬼娃娃(林友赛)找我。
所以发了这篇文章,以CentOS为例配置L2TP/IPsec,其实不单CentOS,其他系列系统(如Ubuntu等)如此配置,L2TP也能正常使用。
首先,安装strongSwan和xl2tpd,不用Openswan是因为据说OSX会连不上。
这个简单,直接yum或apt-get就行了。
以防万一,还是把命令发出来:
yum install strongswan xl2tpd -y
strongSwan主要是为了实现IPsec,而IPsec又是为了PSK,我喜欢这个。
先来配置strongSwan,在/etc/strongswan/ipsec.conf中:
config setup
conn %default
ikelifetime=60m
keylife=20m
rekeymargin=3m
keyingtries=1
conn l2tp
keyexchange=ikev1 #IKE协议版本
left=104.149.65.3 #服务器IP,自己修改为你自己的
leftsubnet=0.0.0.0/0
leftprotoport=17/1701
authby=secret #PSK认证
leftfirewall=no #不允许strongSwan更改防火墙规则
right=%any
rightprotoport=17/%any
type=transport # ipsec transport mode
auto=add
重要的points,我已经写在上面了。基本上都是预设值。
接下来配置PSK密匙,在/etc/strongswan/ipsec.secrets中:
# ipsec.secrets - strongSwan IPsec secrets file : PSK "修改这里为你的PSK密匙"
这样就完成了strongSwan的配置了,接下来配置L2TP(xl2tpd)。
在/etc/xl2tpd/xl2tpd.conf中:
[global] listen-addr = 104.149.65.3 ;服务器IP,自己修改为你自己的,跟strongSwan保持一致 [lns default] ip range = 172.16.37.2-172.16.37.254 ;分配给客户端的ip local ip = 172.16.37.1 ;L2TP本地ip,也是客户端的网关 assign ip = yes require chap = yes refuse pap = yes ;默认就是拒绝pap的,但是如果你用PAM验证的话,那就要注释这句 require authentication = yes name = xl2tpd ppp debug = yes pppoptfile = /etc/ppp/options.xl2tpd length bit = yes
因为172.16.36.X被我分给了PPTP,所以L2TP用了172.16.37.X,这个看自己喜好,不影响。
接下来,编辑/etc/ppp/options.xl2tpd:
ipcp-accept-local ipcp-accept-remote ms-dns 8.8.8.8 ms-dns 8.8.4.4 noccp auth crtscts idle 1800 mtu 1460#这个根据实际,国情应该大部分是1460吧 mru 1460#这个根据实际,国情应该大部分是1460吧 nodefaultroute debug lock proxyarp connect-delay 5000 #login#如果你用了PAP在xl2tpd.conf中的话,那么去掉前面的注释
好了,如果你完全按我上面的配置,那么就是不使用PAP PAM的。
如果你改了用PAP PAM,那么还要修改/etc/pam.d/ppp,改为:
#%PAM-1.0 auth required pam_nologin.so auth required pam_unix.so account required pam_unix.so session required pam_unix.so
这样来达到请求,如果没该用PAP PAM,那就不用改。
以防万一,把原始的/etc/pam.d/ppp配置放上来:
#%PAM-1.0 auth include password-auth account required pam_nologin.so account include password-auth session include password-auth
最后一步,给L2TP添加用户,在/etc/ppp/chap-secrets中,按照如此规则填写,就像PPTP VPN一样。
# Secrets for authentication using CHAP # client server secret IP addresses 用户名 xl2tpd 密码 *
如果你用了PAP,那么记得修改/etc/ppp/pap-secrets,规则同上。
这样就完成了所有的配置,启动strongSwan和xl2tpd:
service strongswan start service xl2tpd start
这样便可正常使用了。
如果你跟我一样,配置了iptables防火墙规则,非许必丢,那么下面这些规则就需要了。
iptables -I INPUT -p udp --dport 500 -j ACCEPT iptables -I INPUT -p udp --dport 4500 -j ACCEPT iptables -I INPUT -p udp -m policy --dir in --pol ipsec -m udp --dport 1701 -j ACCEPT iptables -t nat -A POSTROUTING -s 172.16.37.0/24 -o eth0 -j MASQUERADE iptables -t filter -I FORWARD -s 172.16.37.0/24 -d 172.16.37.0/24 -j DROP iptables -I FORWARD -s 172.16.37.0/24 -j ACCEPT iptables -I FORWARD -d 172.16.37.0/24 -j ACCEPT
以上完整取自我自用的配置,自己看着修改。
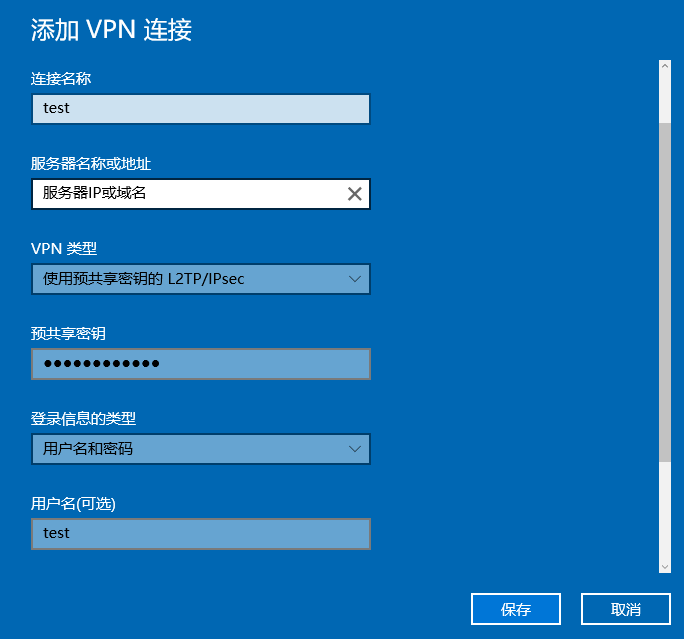
最后给一张Win10创建“使用预共享密钥的L2TP/IPsec”VPN的图:
转载请注明转自:kn007的个人博客的《CentOS配置L2TP/IPsec VPN》

Redirecting to /bin/systemctl start strongswan.service
启动strongswan的时候是这样显示的,这是什么意思,该怎么解决阿,谢谢
@kowldingstan: 正常的啊,centos 6是sysinit,而你的系统是systemd,自然提示不一样。这属于基础问题,自己搜索下就知道了
@kn007: 所以应该怎么解决?
@kowldingstan: 不用解决啊,这又不是报错。
@kn007: 真的? 谢谢
@kn007: 可以不配置iptables么
@kowldingstan: 可以啊
能看见么
@kowldingstan: 啥?
能看见日志么
@kowldingstan: 有什么问题吗?
@kn007: 发不出去
@kowldingstan: 我看到了,有什么问题吗?你这日志太长,没重点,我懒得看。
@kn007: 都连接不上,你知道是怎么回事么
@kowldingstan: 你这样说,我也不清楚。
@kowldingstan: 你发了这么长,没看见错误。
你先看下你防火墙,还有有没有转发流量
@kn007: 关闭么?
@kowldingstan: 自行调试,谢谢
@kn007: 所以是? 你到底能不能给一个准确的答案
@kowldingstan: 你问题出在哪呢?你报错的部分我没看到。
@kn007: 000 using kernel interface: netkey
000 interface lo/lo ::1@500
000 interface lo/lo 1XX.X.0.1@4500
000 interface lo/lo 1XX.X.0.1@500
000 interface enp2s0/enp2s0 1XX.X0.1.51@4500
000 interface enp2s0/enp2s0 1XX.X0.1.51@500
000 interface virbr0/virbr0 1XX.X68.122.1@4500
000 interface virbr0/virbr0 1XX.X68.122.1@500
000
000
000 fips mode=disabled;
000 SElinux=disabled
000
000 config setup options:
000
000 configdir=/etc, configfile=/etc/ipsec.conf, secrets=/etc/ipsec.secrets, ipsecdir=/etc/ipsec.d, dumpdir=/var/run/pluto, statsbin=unset
000 sbindir=/usr/sbin, libexecdir=/usr/libexec/ipsec
000 pluto_version=3.15, pluto_vendorid=OE-Libreswan-3.15
000 nhelpers=0, uniqueids=no, perpeerlog=no, shuntlifetime=900s, xfrmlifetime=300s
000 ddos-cookies-treshold=50000, ddos-max-halfopen=25000, ddos-mode=auto
000 ikeport=500, strictcrlpolicy=no, crlcheckinterval=0, listen=, nflog-all=0
000 secctx-attr-type=32001
000 myid = (none)
000 debug none
000
000 nat-traversal=yes, keep-alive=20, nat-ikeport=4500
000 virtual-private (%priv):
000
000 ESP algorithms supported:
000
000 algorithm ESP encrypt: id=3, name=ESP_3DES, ivlen=8, keysizemin=192, keysizemax=192
000 algorithm ESP encrypt: id=6, name=ESP_CAST, ivlen=8, keysizemin=128, keysizemax=128
000 algorithm ESP encrypt: id=11, name=ESP_NULL, ivlen=0, keysizemin=0, keysizemax=0
000 algorithm ESP encrypt: id=12, name=ESP_AES, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=13, name=ESP_AES_CTR, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=14, name=ESP_AES_CCM_A, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=15, name=ESP_AES_CCM_B, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=16, name=ESP_AES_CCM_C, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=18, name=ESP_AES_GCM_A, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=19, name=ESP_AES_GCM_B, ivlen=12, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=20, name=ESP_AES_GCM_C, ivlen=16, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=22, name=ESP_CAMELLIA, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=252, name=ESP_SERPENT, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm ESP encrypt: id=253, name=ESP_TWOFISH, ivlen=8, keysizemin=128, keysizemax=256
000 algorithm AH/ESP auth: id=1, name=AUTH_ALGORITHM_HMAC_MD5, keysizemin=128, keysizemax=128
000 algorithm AH/ESP auth: id=2, name=AUTH_ALGORITHM_HMAC_SHA1, keysizemin=160, keysizemax=160
000 algorithm AH/ESP auth: id=5, name=AUTH_ALGORITHM_HMAC_SHA2_256, keysizemin=256, keysizemax=256
000 algorithm AH/ESP auth: id=6, name=AUTH_ALGORITHM_HMAC_SHA2_384, keysizemin=384, keysizemax=384
000 algorithm AH/ESP auth: id=7, name=AUTH_ALGORITHM_HMAC_SHA2_512, keysizemin=512, keysizemax=512
000 algorithm AH/ESP auth: id=8, name=AUTH_ALGORITHM_HMAC_RIPEMD, keysizemin=160, keysizemax=160
000 algorithm AH/ESP auth: id=9, name=AUTH_ALGORITHM_AES_XCBC, keysizemin=128, keysizemax=128
000 algorithm AH/ESP auth: id=251, name=AUTH_ALGORITHM_NULL_KAME, keysizemin=0, keysizemax=0
000
000 IKE algorithms supported:
000
000 algorithm IKE encrypt: v1id=0, v1name=0??, v2id=16, v2name=AES_CCM_C, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=0, v1name=0??, v2id=15, v2name=AES_CCM_B, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=0, v1name=0??, v2id=14, v2name=AES_CCM_A, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=5, v1name=OAKLEY_3DES_CBC, v2id=3, v2name=3DES, blocksize=8, keydeflen=192
000 algorithm IKE encrypt: v1id=24, v1name=OAKLEY_CAMELLIA_CTR, v2id=24, v2name=CAMELLIA_CTR, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=8, v1name=OAKLEY_CAMELLIA_CBC, v2id=23, v2name=CAMELLIA_CBC, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=20, v1name=OAKLEY_AES_GCM_C, v2id=20, v2name=AES_GCM_C, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=19, v1name=OAKLEY_AES_GCM_B, v2id=19, v2name=AES_GCM_B, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=18, v1name=OAKLEY_AES_GCM_A, v2id=18, v2name=AES_GCM_A, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=13, v1name=OAKLEY_AES_CTR, v2id=13, v2name=AES_CTR, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=7, v1name=OAKLEY_AES_CBC, v2id=12, v2name=AES_CBC, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=65004, v1name=OAKLEY_SERPENT_CBC, v2id=65004, v2name=SERPENT_CBC, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=65005, v1name=OAKLEY_TWOFISH_CBC, v2id=65005, v2name=TWOFISH_CBC, blocksize=16, keydeflen=128
000 algorithm IKE encrypt: v1id=65289, v1name=OAKLEY_TWOFISH_CBC_SSH, v2id=65289, v2name=TWOFISH_CBC_SSH, blocksize=16, keydeflen=128
000 algorithm IKE hash: id=1, name=OAKLEY_MD5, hashlen=16
000 algorithm IKE hash: id=2, name=OAKLEY_SHA1, hashlen=20
000 algorithm IKE hash: id=4, name=OAKLEY_SHA2_256, hashlen=32
000 algorithm IKE hash: id=5, name=OAKLEY_SHA2_384, hashlen=48
000 algorithm IKE hash: id=6, name=OAKLEY_SHA2_512, hashlen=64
000 algorithm IKE hash: id=9, name=DISABLED-OAKLEY_AES_XCBC, hashlen=16
000 algorithm IKE dh group: id=2, name=OAKLEY_GROUP_MODP1024, bits=1024
000 algorithm IKE dh group: id=5, name=OAKLEY_GROUP_MODP1536, bits=1536
000 algorithm IKE dh group: id=14, name=OAKLEY_GROUP_MODP2048, bits=2048
000 algorithm IKE dh group: id=15, name=OAKLEY_GROUP_MODP3072, bits=3072
000 algorithm IKE dh group: id=16, name=OAKLEY_GROUP_MODP4096, bits=4096
000 algorithm IKE dh group: id=17, name=OAKLEY_GROUP_MODP6144, bits=6144
000 algorithm IKE dh group: id=18, name=OAKLEY_GROUP_MODP8192, bits=8192
000 algorithm IKE dh group: id=22, name=OAKLEY_GROUP_DH22, bits=1024
000 algorithm IKE dh group: id=23, name=OAKLEY_GROUP_DH23, bits=2048
000 algorithm IKE dh group: id=24, name=OAKLEY_GROUP_DH24, bits=2048
000
000 stats db_ops: {curr_cnt, total_cnt, maxsz} :context={0,0,0} trans={0,0,0} attrs={0,0,0}
000
000 Connection list:
000
000 "l2tp-psk": 17X.XX.1.51[11X.XX.XX0.214]:17/1701---17X.XX.1.254...%virtual:17/%any===vhost:?; unrouted; eroute owner: #0
000 "l2tp-psk": oriented; my_ip=unset; their_ip=unset
000 "l2tp-psk": xauth info: us:none, them:none, my_xauthuser=[any]; their_xauthuser=[any]
000 "l2tp-psk": modecfg info: us:none, them:none, modecfg policy:push, dns1:unset, dns2:unset, domain:unset, banner:unset;
000 "l2tp-psk": labeled_ipsec:no;
000 "l2tp-psk": policy_label:unset;
000 "l2tp-psk": ike_life: 28800s; ipsec_life: 3600s; rekey_margin: 540s; rekey_fuzz: 100%; keyingtries: 3;
000 "l2tp-psk": retransmit-interval: 500ms; retransmit-timeout: 60s;
000 "l2tp-psk": sha2_truncbug:yes; initial_contact:no; cisco_unity:no; send_vendorid:no;
000 "l2tp-psk": policy: PSK+ENCRYPT+DONT_REKEY+IKEV1_ALLOW+IKEV2_ALLOW+SAREF_TRACK+IKE_FRAG_ALLOW;
000 "l2tp-psk": conn_prio: 32,32; interface: enp2s0; metric: 0; mtu: unset; sa_prio:auto; nflog-group: unset;
000 "l2tp-psk": dpd: action:clear; delay:40; timeout:130; nat-t: force_encaps:no; nat_keepalive:yes; ikev1_natt:both
000 "l2tp-psk": newest ISAKMP SA: #0; newest IPsec SA: #0;
000 "l2tp-psk-nonat": 1XX.X0.1.51[1XX.X1.1XX.X14]:17/1701---1XX.X0.1.254...%any:17/%any; unrouted; eroute owner: #0
000 "l2tp-psk-nonat": oriented; my_ip=unset; their_ip=unset
000 "l2tp-psk-nonat": xauth info: us:none, them:none, my_xauthuser=[any]; their_xauthuser=[any]
000 "l2tp-psk-nonat": modecfg info: us:none, them:none, modecfg policy:push, dns1:unset, dns2:unset, domain:unset, banner:unset;
000 "l2tp-psk-nonat": labeled_ipsec:no;
000 "l2tp-psk-nonat": policy_label:unset;
000 "l2tp-psk-nonat": ike_life: 28800s; ipsec_life: 3600s; rekey_margin: 540s; rekey_fuzz: 100%; keyingtries: 3;
000 "l2tp-psk-nonat": retransmit-interval: 500ms; retransmit-timeout: 60s;
000 "l2tp-psk-nonat": sha2_truncbug:yes; initial_contact:no; cisco_unity:no; send_vendorid:no;
000 "l2tp-psk-nonat": policy: PSK+ENCRYPT+DONT_REKEY+IKEV1_ALLOW+IKEV2_ALLOW+SAREF_TRACK+IKE_FRAG_ALLOW;
000 "l2tp-psk-nonat": conn_prio: 32,32; interface: enp2s0; metric: 0; mtu: unset; sa_prio:auto; nflog-group: unset;
000 "l2tp-psk-nonat": dpd: action:clear; delay:40; timeout:130; nat-t: force_encaps:no; nat_keepalive:yes; ikev1_natt:both
000 "l2tp-psk-nonat": newest ISAKMP SA: #0; newest IPsec SA: #0;
000
000 Total IPsec connections: loaded 2, active 0
000
000 State Information: DDoS cookies not required, Accepting new IKE connections
000 IKE SAs: total(0), half-open(0), open(0), authenticated(0), anonymous(0)
000 IPsec SAs: total(0), authenticated(0), anonymous(0)
000
000 Bare Shunt list:
000
我发完了以后为什么不显示
@kowldingstan: 不是,你发这么长,有什么意义吗?
又没报错
@kn007: 为什么连不上
@kowldingstan: 我也不知道,你这样我也定位不到问题
@kn007: 需不需要添加协议或者证书
@kowldingstan: 你直接用手机挂4G试试嘛,会不会你家里原因,还有确认下转发正不正常
@kn007: 试了,ios过了一两秒就显示连接不上,我怀疑是防火墙的问题,可是我都关闭了,不过要是连接超时也得等个一分钟将近
试了,ios过了一两秒就显示连接不上,我怀疑是防火墙的问题,可是我都关闭了,不过要是连接超时也得等个一分钟将近
@kowldingstan: 会不会运营商问题,你确定你服务器防火墙都是禁用的吧?
@kn007: 是的,之前我用openswan都可以
@kowldingstan: 你连接后,外部请求日志是怎么样的?
@kowldingstan: 我看你这日志,感觉不像是用我配置,你需要注意下ubuntu,debian、centos的配置不一样的。要根据实际编辑。
按照流程操作下来,但是连不上
Failed to establish a VPN connection.
IPSec connection failed
能否把相关debug方法贴出来,log都不知道看哪个
@Samuel: 不同系统,日志位置不同。你看syslog位置,像centos是/var/log/messages,在里面就有日志。
我查了很多资料,我想在 ip range里面设置两个ip段
一直没弄好